This application automates the issuance and renewal of ACME SSL/TLS certificates. The certificates are stored inside Azure Key Vault. Many Azure services such as Azure App Service, Application Gateway, CDN, etc. are able to import certificates directly from Key Vault.
We have started to address the following requirements:
- Use the Azure Key Vault to store SSL/TLS certificates securely
- Centralize management of a large number of certificates using a single Key Vault
- Easy to deploy and configure solution
- Highly reliable implementation
- Ease of Monitoring (Application Insights, Webhook)
Key Vault allows for secure and centralized management of ACME certificates.
Key Vault Acmebot v3 has been released since December 31, 2019. Users deploying earlier than this are encouraged to upgrade to v3 by following the ugprade process described here:
As of August 2020, Azure CDN / Front Door does not automatically deploy new Key Vault certificates. I develop an utility application to automatically deploy a new version of the certificate.
https://github.com/shibayan/keyvault-certificate-rotation
- All Azure App Services (Web Apps / Functions / Containers, regardless of OS)
- Azure CDN and Front Door
- Azure Application Gateway v2
- Issuing certificates with SANs (subject alternative names) (one certificate for multiple domains)
- Issuing certificates and wildcard certificates for Zone Apex domains
- Automated certificate renewal
- ACME-compliant Certification Authorities
You will need the following:
- Azure Subscription (required to deploy this solution)
- Azure Key Vault (existing one or new Key Vault can be created at deployment time)
- DNS provider (required to host your public DNS zone)
- Azure DNS
- Cloudflare
- GratisDNS
- Email address (required to register with ACME)
For Azure Cloud
For Azure China
For Azure Government
Update the following configuration settings of the Function App:
- Acmebot:VaultBaseUrl
- DNS name of the Azure Key Vault (if you are using an existing Key Vault)
- Acmebot:Webhook
- Webhook destination URL (optional, Slack and Microsoft Teams are recommended)
There are also additional settings that will be automatically created by Key Vault Acmebot
- Acmebot:Endpoint
- The ACME endpoint used to issue certificates
- Acmebot:Contacts
- The email address (required) used in ACME account registration
- Acmebot:AzureDns:SubscriptionId
- Your Azure subscription ID in order to identify which DNS resources can be used for ACME
You must enable Authentication on the Function App that is deployed as part of this application.
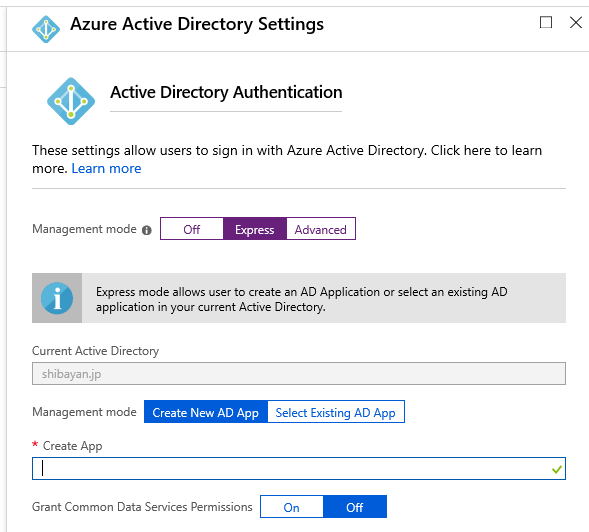
Open the Azure Portal, navigate to the Authentication / Authorization menu of the deployed Function App and enable App Service authentication. Select the Login with Azure Active Directory as the action to perform if the request is not authenticated. We recommend using Azure Active Directory as your authentication provider, but it works with other providers as well, although it's not supported.
Select Azure Active Directory as the authentication provider, select Express as the management mode, and select OK.
Finally, you can save your previous settings to enable App Service authentication.
Open the Access Control (IAM) of the target DNS zone or resource group containing the DNS zone, and assign the role of DNS Zone Contributor to the deployed application.
When using a DNS provider other than Azure DNS, please refer to the following page for configuration.
https://github.com/shibayan/keyvault-acmebot/wiki/DNS-Provider-Configuration
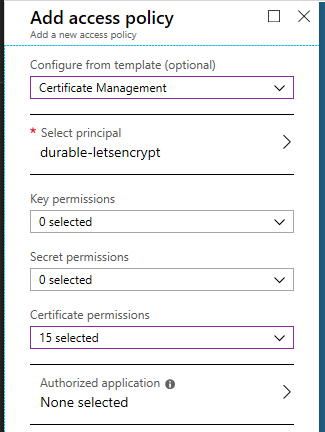
Open the access policy of the Key Vault and add the Certificate management access policy for the deployed application.
Access https://YOUR-FUNCTIONS.azurewebsites.net/add-certificate with a browser and authenticate with Azure Active Directory and the Web UI will be displayed. Select the target domain from that screen, add the required subdomains, and run, and after a few tens of seconds, the certificate will be issued.
If the Access Control (IAM) setting is not correct, nothing will be shown in the drop-down list.
All existing ACME certificates are automatically renewed 30 days before their expiration.
The default check timing is 00:00 UTC. If you need to change the time zone, use WEBSITE_TIME_ZONE to set the time zone.
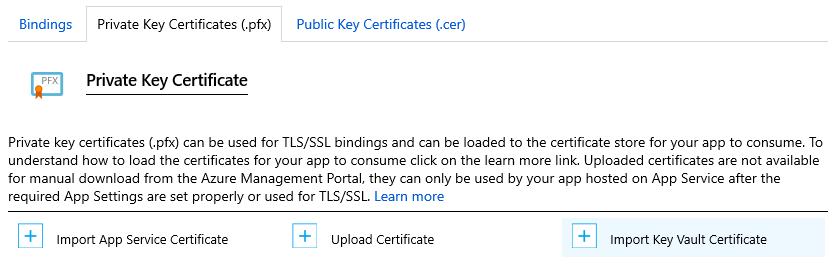
You can import the Key Vault certificate to the App Service by opening the TLS/SSL Settings from Azure Portal and selecting the Import Key Vault Certificate button from the Private Key Certificate (.pfx).
After importing, the App Service will automatically check for certificate updates.
The issued certificate can be downloaded from Key Vault and used elsewhere, either in Azure or outside Azure.
To Remove a certificate from the system delete it from the Key Vault. Key Vault Acmebot will no longer renew the certificate.
To Reinstall or Upgrade Key Vault Acmebot without removing your certificates, ensure that the Key Vault is not removed. Key Vault Acmebot will use the exisiting certificates and vault after upgrade or reinstall
- ACMESharp Core by @ebekker
- Durable Functions by @cgillum and contributors
- DnsClient.NET by @MichaCo
This project is licensed under the Apache License 2.0