Q1. According to the shared responsibility model, which cloud computing model places the most responsibility on the cloud service provider (CSP)?
- Hybrid Cloud
- Software as a Service (SaaS)
- Platform as a Service (PaaS)
- Infrastructure as a Service (IaaS)
- PaaS
- public cloud
- private cloud
- IaaS
Q3. Your organization recently implemented a unified messaging solution and VoIP phones on every desktop. You are responsible for researching the vulnerabilities of the VoIP system. Which type of attack are VoIP phones most vulnerable to experiencing?
- denial-of-service
- brute force attacks
- malware
- buffer overflow
- cloud access security broker (CASB)
- intrusion prevention system (IPS)
- intrusion detection system (IDS)
- next generation firewall
- SIEM
- UTM
- protocol analyzer
- data sink
- code review
- code analysis
- static analysis
- dynamic analysis
Q7. Which option describes testing that individual software developers can conduct on their own code?
- gray box testing
- integration testing
- white box testing
- unit testing
Q8. In black box penetration testing, what information is provided to the tester about the target environment?
- none
- limited details of server and network infrastructure
- all information
- limited details of server infrastructure
Q9. Which security control can best protect against shadow IT by identifying and preventing use of unsanctioned cloud apps and services?
- intrusion prevention system (IPS)
- next generation firewall
- cloud access security broker (CASB)
- intrusion detection system (IDS)
- monitoring of normal employee system and data access patterns
- applying system and application updates regularly
- fault tolerant infrastructure and data redundancy
- separation of duties and job rotation
Q11. During a penetration test, you find a file containing hashed passwords for the system you are attempting to breach. Which type of attack is most likely to succeed in accessing the hashed passwords in a reasonable amount of time?
- rainbow table attack
- pass-the-hash attack
- password spray attack
- brute force attack
Explanation: A rainbow table attack is a more efficient and effective way of cracking many hashed passwords, whereas brute-forcing would take much longer and may not complete in a reasonable amount of time. ref
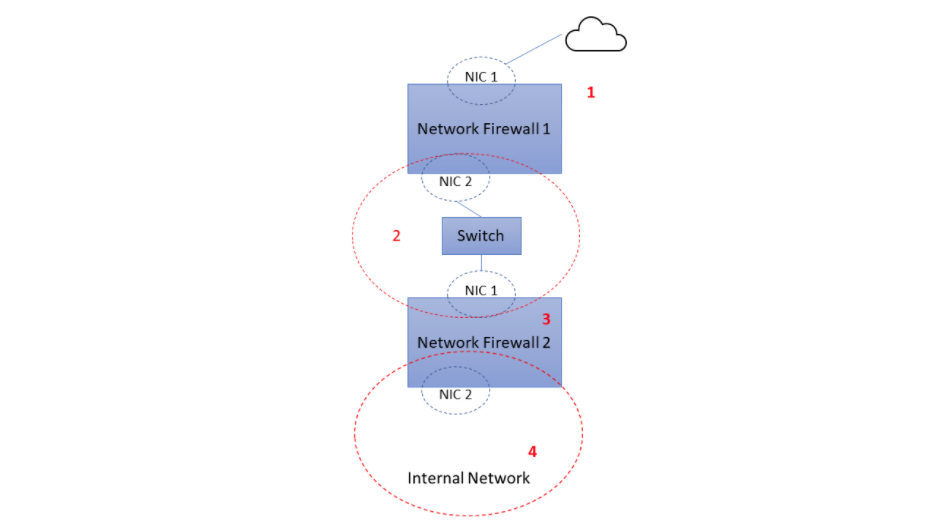
- 4
- 1
- 2
- 3
Q13. You configure an encrypted USB drive for a user who needs to deliver a sensitive file at an in-person meeting. What type of encryption is typically used to encrypt the file?
- file hash
- asymmetric encryption
- digital signature
- symmetric encryption
- DRP works to keep a business up and running despite a disaster. BCP works to restore the original business capabilities.
- BCP works to keep a business up and running despite a disaster. DRP works to restore the original business capabilities.
- BCP is part of DRP.
- DRP is part of BCP.
- non-repudiation
- integrity
- availability
- confidentiality
Source: LinkedIn assessment practice mode
Q16. You need to recommend a solution to automatically assess your cloud-hosted VMs against CIS benchmarks to identify deviations from security best practices. What type of solution should you recommend?
- Cloud Security Posture Management (CSPM)
- Intrusion Detection and Prevention System (IDPS)
- Cloud Workload Protection Platforms (CWPP)
- Cloud Access Security Brokers (CASBs)
Source: LinkedIn assessment practice mode
- Compression
- Hashing
- Symmetric encryption
- Stenography
- CCPA
- GDPR
- NIST Privacy Framework
- OSPF
Q19. what is the term for the policies and technologies implemented to protect, limit, monitor, audit, and govern identities with access to sensitive data and resources?
- identity and access management (IAM)
- privileged account management (PAM)
- authentication and authorization
- least privilege
Q20. You have configured audit settings in your organization's cloud services in the event of a security incident. What type of security control is an audit trail?
- preventive control
- detective control
- directive control
- corrective control
- grayout
- blackout
- brownout
- whiteout
Q22. Your security team recommends adding a layer of defense against emerging persistent threats and zero-day exploits for all endpoints on your network. The solution should offer protection from external threats for network-connected devices, regardless of operating system. Which solution is best suited to meet this requirement?
- Security Information Event Management (SIEM)
- Extended Detection and Response (XDR)
- next generation firewall (NGFW)
- Cloud App Security Broker (CASB)
- TRIKE
- TOGAF
- STRIDE
- MITRE ATT&CK
Q24. You organization is conducting a pilot deployment of a new e-commerce application being considered for purchase. You need to recommend a strategy to evaluate the security of the new software. Your organization does not have access to the application's source code.
- dynamic application security testing
- unit testing
- white box testing
- static application security testing
Q25. You need to disable the camera on corporate devices to prevent screen capture and recording of sensitive documents, meetings, and conversations. Which solution would be be suited to the task?
- Mobile Device Management (MDM)
- Data Loss Prevention (DLP)
- Intrusion Detection and Prevention System (IDPS)
- cloud access security broker (CASB)