-
Notifications
You must be signed in to change notification settings - Fork 57
SharePoint Online addin only authentication
This type of authentication uses addin only policy and OAuth bearer tokens for authenticating http requests.
-
clientId- required string, client id obtained when registering the addin -
clientSecret- required string, client secret obtained when registering the addin -
realm- optional string, your SharePoint Online tenant id. You can leave it empty or fill in, that will add small (really small) performance improvement. The easiest way to find tenant is to open SharePoint Online site collection, click Site Settings -> Site App Permissions. Under this page you wll see at least one app "Microsoft.SharePoint". The tenant id (realm) is highlighted in the image below:
{
clientId: '28bq7e56-8c3a-487d-hbfb-ef1a74539cbe',
clientSecret: 's6LZ4VvoeKOS+MyAhklcavsyJBF4XhWo06OgY6czYJ0=',
realm: '85e5f09b-4c17-4d80-afea-260bb171c456'
}{
headers: {
'Authorization': 'Bearer <token>'
}
}For this authentication to work you need to register new addin inside SharePoint Online.
Steps:
-
Open SharePoint Online app registration page,
https://contoso.sharepoint.com/sites/dev/_layouts/15/appregnew.aspx -
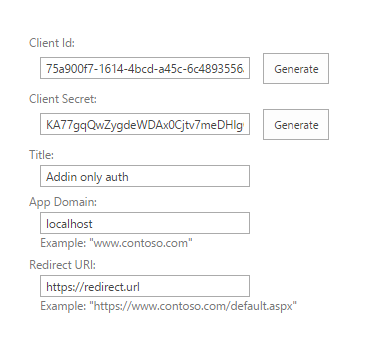
Click on 'Generate' for Client id and Client Secret, fill in Title, App Domain, Redirect URI (you can type in any values you want)
-
Click on 'Create' and save generated Client Id and Client Secret
-
Now you need to apply permissions to the newly registered app. If you want to register the app once and use it for any site collection, it's better to apply tenant scope permissions, so you can use this credentials everywhere inside your SharePoint tenant. In order to apply tenant scoped permissions, open
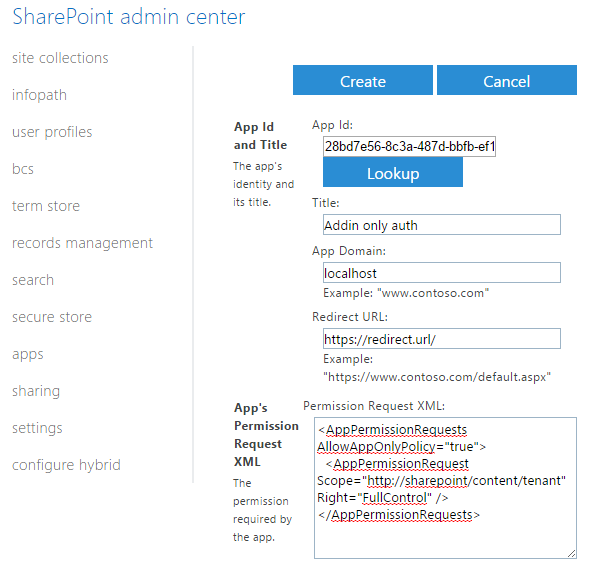
AppInv.aspxpage under SharePoint adminstration web site, i.e.https://[organizaiton]-admin.sharepoint.com/_layouts/15/appinv.aspx, copy paste Client Id from step 3 into App Id field and click 'Lookup'. -
You will see your registerd app, paste in following xml into the 'Permission Request XML:' field and click 'Create' (note: tenant administrator rights required):
<AppPermissionRequests AllowAppOnlyPolicy="true"> <AppPermissionRequest Scope="http://sharepoint/content/tenant" Right="FullControl" /> </AppPermissionRequests>
-
You will see addin 'Trust' confirmation, click on 'Trust It':

if trust-it button is not enabled and you get a red label saying tenant admin needs to trust the app, go back and try again in a few minutes.
-
Now you can use client id and client secret to send authenticated http requests across your SharePoint tenant.
-
If you don't have tenant administrator rights, you can register the app on regular site collection by using url
https://contoso.sharepoint.com/sites/dev/_layouts/15/appinv.aspx. In this case you are not able to use tenant scoped permissions and can only apply site collection permissions:<AppPermissionRequests AllowAppOnlyPolicy="true"> <AppPermissionRequest Scope="http://sharepoint/content/sitecollection" Right="FullControl" /> </AppPermissionRequests>
You need to do that for every site collection you want to send http queries.
import * as spauth from 'node-sp-auth';
import * as request from 'request-promise';
spauth
.getAuth('https://[organization].sharepoint.com/sites/dev/', {
clientId: '28bd7e56-8c3a-487d-bbfb-ef1a74539cbe',
clientSecret: '[your secret]',
realm: '85e5f09b-4c17-4d80-afea-260bb171c456'
})
.then(data => {
var headers = data.headers;
headers['Accept'] = 'application/json;odata=verbose';
request.get({
url: 'https://[organization].sharepoint.com/sites/dev/_api/web',
headers: headers,
json: true
}).then(response => {
console.log(response.d.Title);
});
});- SharePoint Online
- SharePoint on-premise (2013, 2016, 2019)
- ADFS user credentials
- On demand authentication